We have recently released version 3.5 of application traceroute, with an excellent ability to reconstruct the technological stack but smart crawler remained behind and let's face the detection ability lets you want.

But, as always, the works do not stop and continue to develop/test/produce... We are developing version 4.0 where we introduced super algorithms (Baesyan, Shannon Entropy, Advanced Taxonomy etc etc.) worthy of Stanford or MIT (without exaggerating...) and we have definitely improved both traceroute and smart crawler, now I want to show you the latest test results on https://testphp.vulnweb.com. Looking on the net for reports available for vulnweb what shows more findings is that of Acunetix (acunetix!!!) with 39 confirmed vulnerabilities but some of little interest such as php dated, cookies and other minor vulnerabilities.

Smart crawler has discovered and confirmed 32, i.e. a result close to that of blasoned tools, without spending a € .
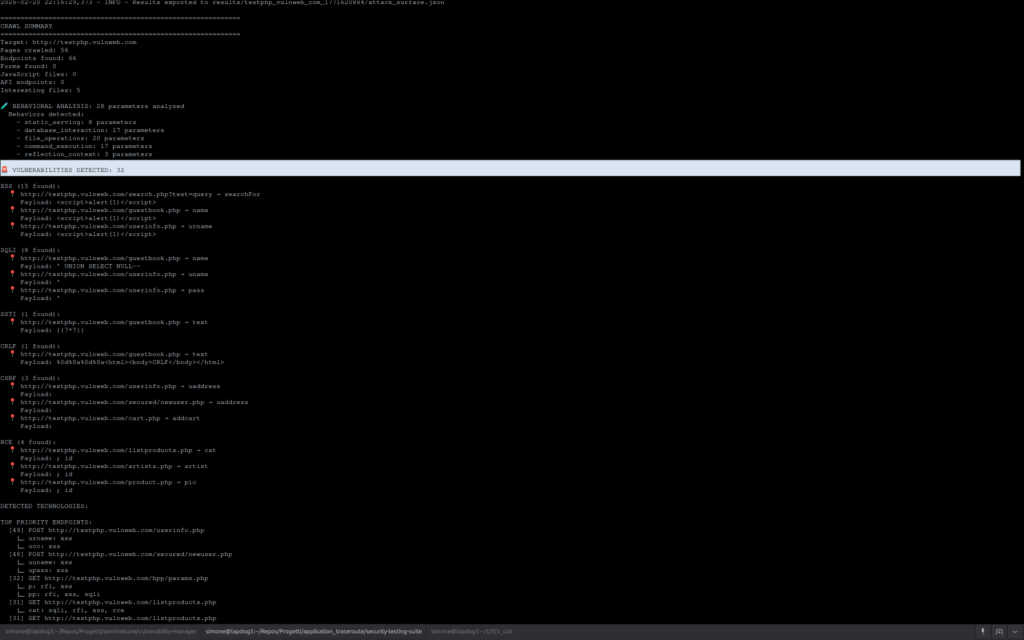
It should also be remembered that the same injection point (i.e. the same parameter encountered by the crwaler) is no longer tested (skip) if it has already been met using this logic:
There is no fixed "short number" — the system uses a unique URL limit on which to test the same parameter for the same vulnerability. Once the limit is reached, the parameter is always skippato.
Basic limits for unique URLs:
| Type | URL max |
|---|---|
| R | 30 |
| SQLi | 28 |
| XXE / SSTI / LFI | 25 |
| LDAPi / XPath | 22 |
| Open Redirect / others | 20 |
| CRLF | 18 |
| XSS / CSRF | 15 |
Then multipliers are applied:
- Confidence ≥ 80% → +30% (e.g. SQLi becomes 36)
- Confidence ≥ 65% → +15%
- Confidence < 45% → -30%
- Website > 100 endpoint → scale up to +50%
- Site < 10 endpoint → minimum guaranteed to 25 Logic for identical URLs: the parameter is skippato immediately if it has already been tested on the same URL (same
schema+host+path, without string query), regardless of the limit.
This speeds up scanning very quickly, avoiding unnecessary waste of time. The use is always, you can use first application traceroute to detect the technology stack and generate valid bypasses in json format which can then be taken as smart crawler input or you can run it directly without bypass.

An interesting feature that I would like to highlight is the management of wordlists and payloads. I am usually using the classic SecList, Fuzzdb and PayloadAllTheThings, I have all under a directory and I pass the path as argument to smart crawler, but if you have a personal directory and subdirectories named them with the names of vulns (lfi, xss, sqli etc) and the files within them will appoint them with something like sqli mysql.txt | uniq" will also create changes in payloads by feeding an internal list of the most useful.
If you want to test the first stable version:
git clone https://github.com/Dognet-Technologies/application_traceroute.git
cd application_traceroute
git checkout v4.0-suite-stable
python3 -m venv venv
source /venv/bin/activate
pip install -r requirements.txt
cd security-testing-suiteNow you have your virtual environment and you can call the tool directly without launching the script. Version 4.0 represents a very important step forward and is in constant active development and you can have new features and bug fixes within a few hours so be patient if you find bugs or if at the time when cloning the repository there are errors, try again after an hour and you will probably have the working tool. Until the stable release there are commits on commit!
We have implemented the licensing system, if you want to test version 4.0 you can use this key:
DOGNETX0EV-8IAM-AW64-DJNZfreeIf you are interested in the version with GUI (it has some extra features such as advanced reporting, graphic reconstruction with technology stack and description) contact us by email to info@dognet.tech or contact the sales team below!
CONTACT US